TCP/IP vs OSI Model Explained
In the world of cybersecurity, understanding how data travels across networks is fundamental. Two key models that describe this process are the TCP/IP model and the OSI model. Let’s break them down simply, so you get the core concepts quickly.
What is TCP/IP?
TCP/IP stands for Transmission Control Protocol/Internet Protocol. It’s the basic communication language of the internet and most computer networks. It defines how data should be packetized, addressed, transmitted, routed, and received.
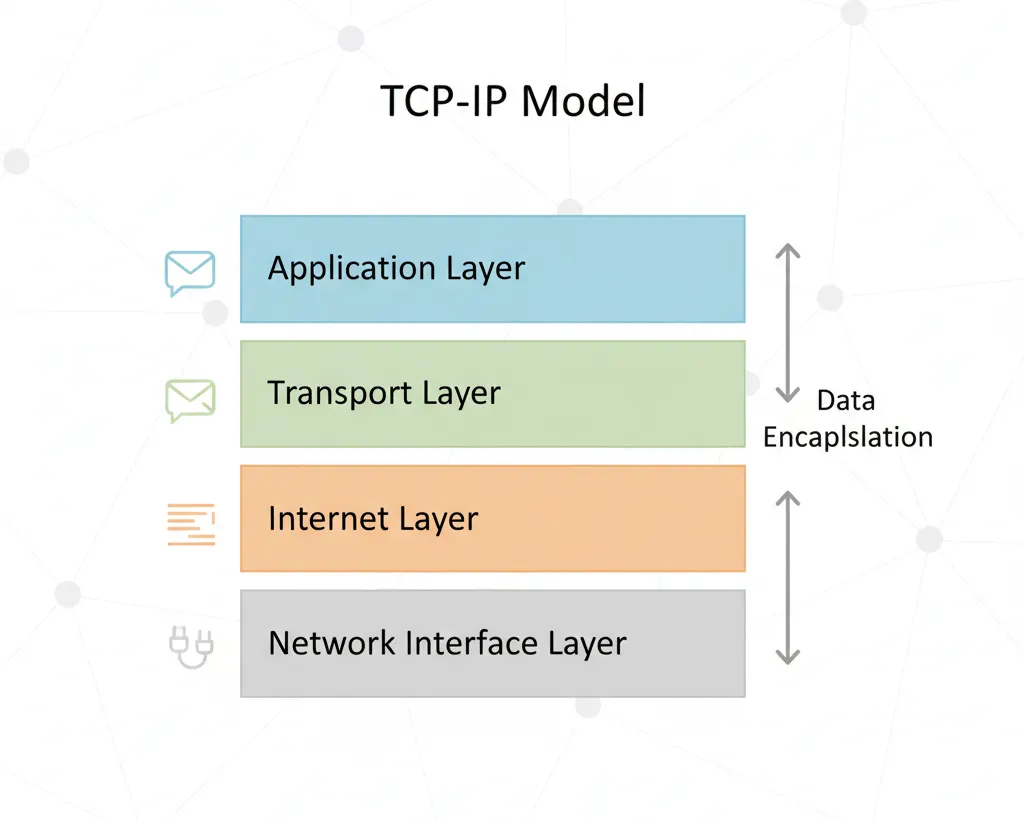
TCP/IP is built around four layers:
- Application Layer: Where network applications like web browsers, email clients, and FTP operate. It handles protocols such as HTTP, FTP, and SMTP.
- Transport Layer: Responsible for data transport, ensuring complete data transfer with protocols like TCP (reliable connection) and UDP (faster but without error-checking).
- Internet Layer: Handles logical addressing and routing with the IP protocol; this is where your device’s IP address comes into play.
- Network Access Layer: Manages hardware addressing and the details of the physical transmission over the network, including Wi-Fi, Ethernet, and other network interfaces.
What is the OSI Model?
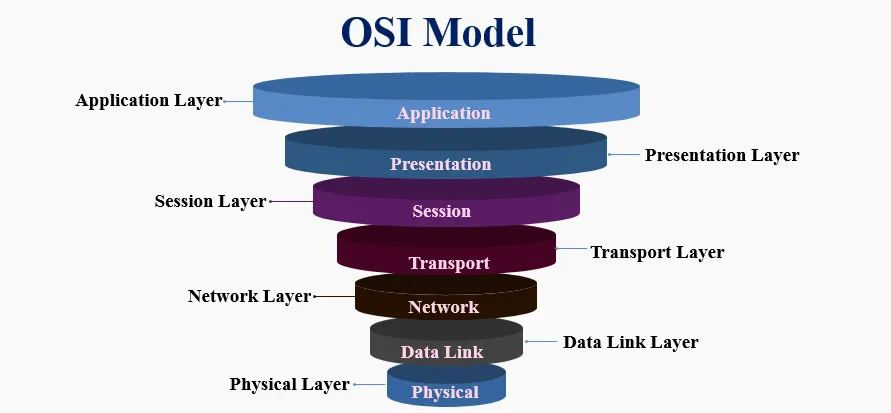
The Open Systems Interconnection (OSI) model is a conceptual framework used to understand and design network systems. It divides the network communication process into seven distinct layers:
- Physical Layer: Deals with the physical hardware, cables, and signals.
- Data Link Layer: Manages error detection, framing, and physical addressing (MAC addresses).
- Network Layer: Responsible for routing and logical addressing (IP addresses).
- Transport Layer: Ensures reliable data transfer (TCP/UDP).
- Session Layer: Manages sessions or connections between applications.
- Presentation Layer: Translates data formats, handles encryption and compression.
- Application Layer: Interface for end-user applications and network services.
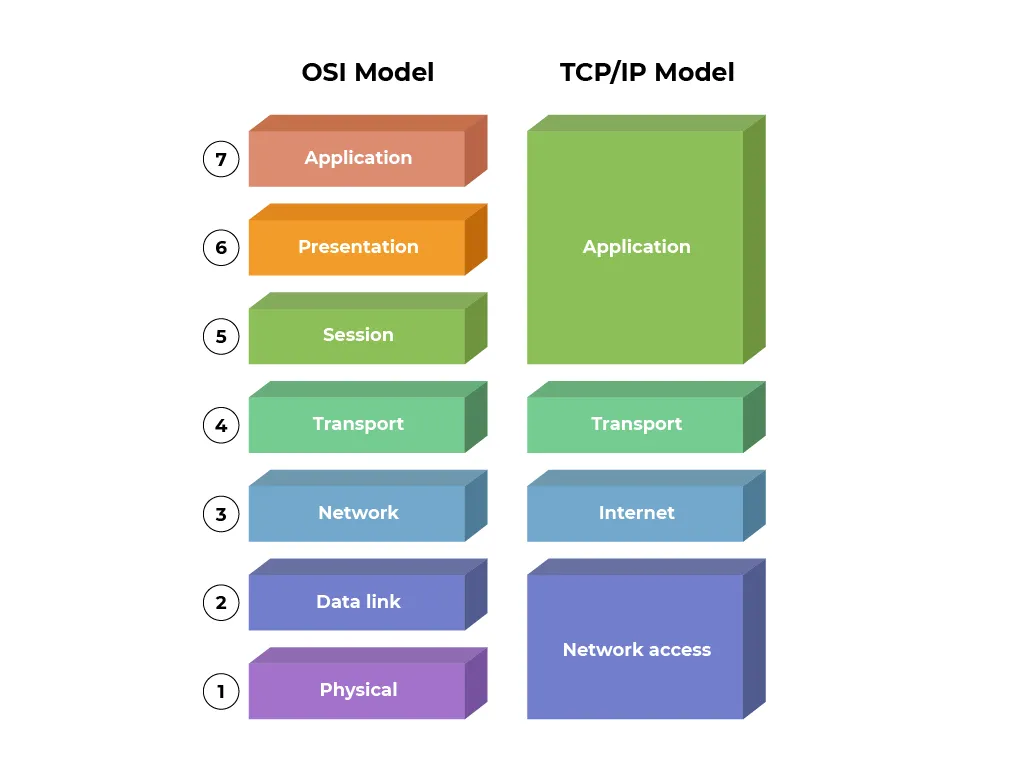
TCP/IP vs OSI (Side by Side)
Why Do These Models Matter?
In cybersecurity, knowing how data travels is like knowing the blueprint of a house before protecting it. Attackers exploit weaknesses at different layers, and defenders use tools designed for specific layers. For example:
- A DDoS attack often targets the Network or Transport layer.
- Phishing emails exploit weaknesses at the Application layer.
- Wi-Fi sniffing attacks hit the Physical and Data Link layers.
By mastering TCP/IP and OSI, you’ll know exactly where and how to defend.
Real-World Example: Sending a WhatsApp Message
- Application Layer: You type
Helloin WhatsApp, which uses an application protocol. - Transport Layer: WhatsApp uses TCP to ensure your message is delivered correctly.
- Network/Internet Layer: The message is wrapped with your device’s IP and the server’s IP. Routers decide the best path.
- Data Link & Physical/Network Access Layer: Your Wi-Fi/Ethernet card converts it into electrical/optical signals or radio waves.
Seconds later, your friend sees the message pop up. Magic? Not really just protocols doing their job.
Cybersecurity Perspective
- Firewalls: Work mainly at the Network and Transport layers to block/allow traffic.
- Intrusion Detection Systems (IDS): Monitor multiple layers for suspicious patterns.
- Encryption (TLS/SSL): Operates at the Presentation layer to protect Application data.
- ARP Spoofing Attacks: Exploit the Data Link layer.
Knowing the layer helps you pinpoint where the attack happens and which defense tool to use.
Keep exploring, stay curious, and secure your networks.
Copyright © 2026 Mahidul Haque. This post is licensed under a CC BY-NC-ND 4.0 license. You may read, learn, and share links to this post for non‑commercial, educational purposes, as long as you give appropriate attribution. You may not copy, reproduce, adapt, distribute, or use this work commercially without explicit permission.